Mcp Server Security Best Practices

Built for Speed: ~10ms Latency, Even Under Load
Blazingly fast way to build, track and deploy your models!
- Handles 350+ RPS on just 1 vCPU — no tuning needed
- Production-ready with full enterprise support
The Model Context Protocol (MCP) is quickly becoming the backbone of how Large Language Models (LLMs) securely connect with enterprise data, tools, and workflows. But with great flexibility comes serious responsibility—an insecure MCP Server can expose sensitive systems and data to breaches, prompt injections, or malicious actors.
In this guide, we’ll walk through MCP Server security best practices, and show how the TrueFoundry MCP Gateway helps enterprises implement these guardrails by default.
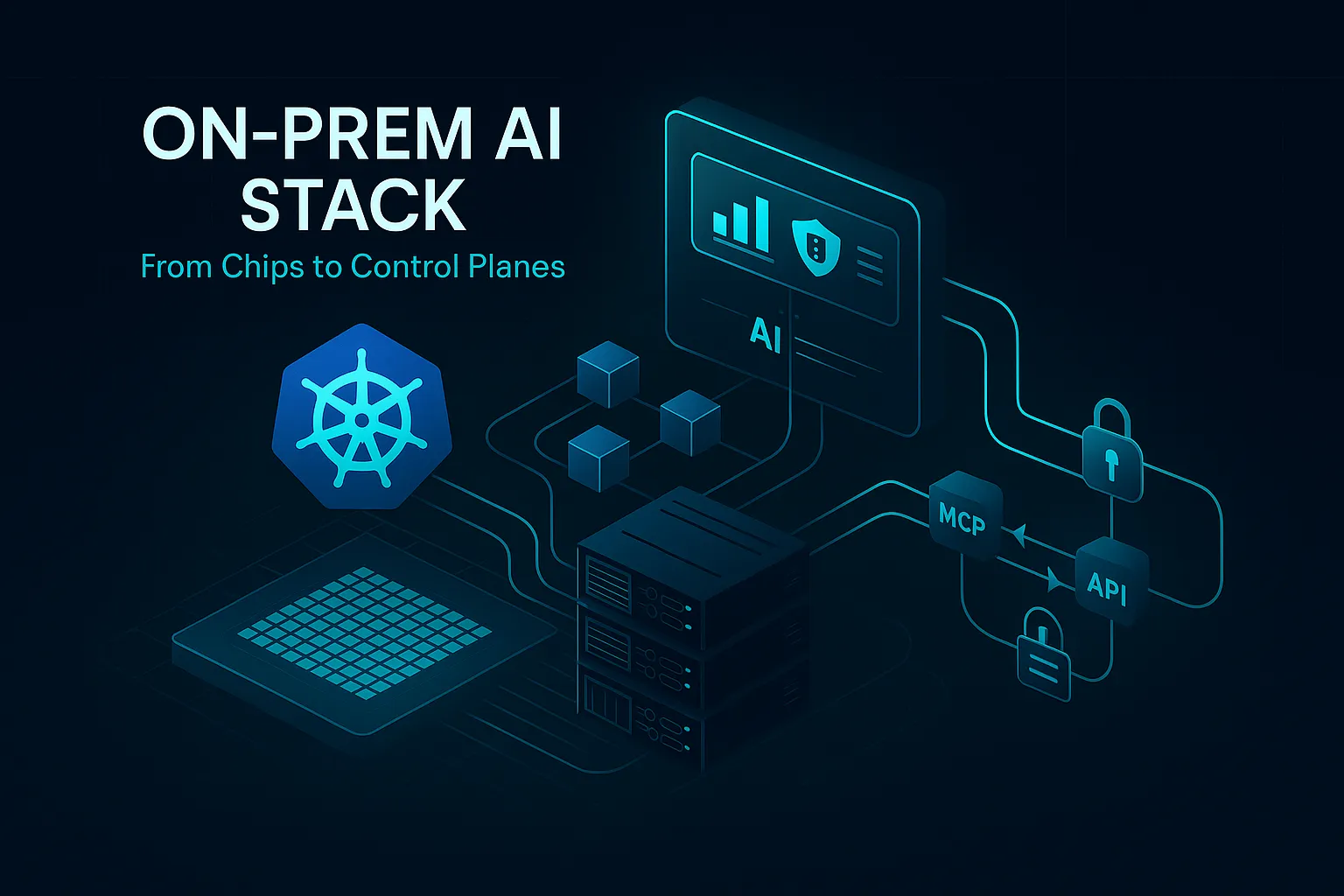
What Is MCP Server?
An MCP Server (Model Context Protocol Server) is a secure middleware layer that connects AI models with external tools, data sources, and enterprise systems. It acts as a controlled gateway, allowing AI applications to access real-time information and perform actions while enforcing authentication, authorization, and governance policies.
In simple terms, an MCP server ensures that AI systems interact with your infrastructure safely and reliably. Instead of giving AI direct access to databases or APIs, the MCP server validates requests, applies role-based permissions, and logs activity for compliance.
Why MCP Servers Matter
- Security: Prevents unauthorized access to sensitive data
- Governance: Tracks usage through logs and audit trails
- Scalability: Standardizes how AI tools connect to services
- Compliance: Helps meet enterprise security and regulatory requirements
Common Use Cases
- Connecting AI assistants to internal company tools
- Enabling secure data retrieval from enterprise databases
- Automating workflows with controlled AI actions
Why Securing MCP Servers Is Critical
MCP Servers act as the bridge between AI agents and your enterprise systems—databases, APIs, internal tools. Without proper safeguards:
- Unauthorized users may gain access to sensitive data.
- Agents could misuse tools (e.g., deleting records, escalating privileges). Agents might delete records, escalate privileges, or trigger unsafe actions. Gartner predicts that by 2026, 75% of organizations will adopt AI security tools to prevent misuse【Gartner Emerging Technologies Report, 2023】
- Malicious MCP servers could trick agents into leaking data.A rogue MCP server could trick agents into leaking confidential data. According to MITRE, prompt injection attacks are among the top emerging AI threats【MITRE ATLAS, 2024】
Strong MCP security is not optional—it’s the foundation of trustworthy AI adoption.
Core MCP Server Security Best Practices
1. Strong Authentication
- Use OAuth 2.0 / OIDC with enterprise identity providers (Okta, Azure AD, Auth0).
- Avoid static tokens in production—they’re difficult to rotate and audit.
- Enforce short-lived tokens and PKCE for added resilience against interception.
- Where possible, integrate with federated identity for SSO and centralized control.
In the TrueFoundry MCP Gateway, servers can be protected with OAuth 2.0 or Personal Access Tokens, while supporting enterprise IdPs out of the box.
2. Fine-Grained Authorization (RBAC)
- Implement role-based access control: e.g., viewer, user, admin.
- Assign tool-level permissions so only authorized roles can trigger sensitive actions.
- Follow the principle of least privilege—never expose more than what’s necessary.
TrueFoundry allows administrators to enforce RBAC directly at the MCP Gateway, ensuring tool access is restricted per user or team.
3. Input Validation & Schema Enforcement
- Validate all incoming JSON-RPC requests against schemas.
- Reject malformed inputs or unrecognized parameters to prevent prompt injection attacks.
- Sanitize data before execution, especially when tools perform database or file operations.
The MCP Gateway supports schema-driven validation, helping enforce safe interactions automatically.
4. Observability & Governance
- Enable structured audit logs—who accessed what, when, and why.
- Monitor latency, errors, and usage patterns to detect anomalies.
- Apply rate limits to prevent abuse or runaway agent loops.
- Track cost usage when LLM calls are tied to billing.
With TrueFoundry, every request is logged and observable with dashboards for compliance and governance.
5. Runtime AI Security
Traditional perimeter controls aren’t enough for AI workloads. MCP Servers must be protected at runtime, where LLMs interact with real data, APIs, and user requests. This is where runtime AI security becomes essential:
- Runtime Threat Detection: Monitor live agent-tool interactions to detect anomalies such as prompt injection, data exfiltration, or malicious tool execution.
- Inline Policy Enforcement: Apply guardrails dynamically—block sensitive data leakage, stop unauthorized write/delete operations, and enforce compliance rules in real-time.
- Data Loss Prevention (DLP): Prevent MCP tools from unintentionally exposing PII, financial data, or confidential IP.
The TrueFoundry MCP Gateway integrates with leading runtime security providers like Palo Alto Prisma and other enterprise security platforms. This means organizations can extend their existing Zero Trust and runtime security policies to MCP servers, without building custom solutions.
With this model, you don’t just configure static policies—you gain continuous runtime protection, aligned with your broader enterprise security stack.
6. Secure Deployment Models
- Run MCP servers in isolated environments (VPCs, namespaces, or containers).
- Avoid exposing servers directly to the public internet unless absolutely required.
- For compliance needs, deploy MCP servers in air-gapped or hybrid environments.
TrueFoundry supports flexible deployment—cloud, on-prem, VPC, or air-gapped—so teams can enforce data sovereignty and compliance easily.
Security Challenges In MCP
While MCP (Model Context Protocol) servers enable secure and structured communication between AI models and enterprise systems, they also introduce new security challenges. Because MCP acts as a gateway to sensitive tools, APIs, and data, any weakness in its design or configuration can expose critical resources.
Understanding these challenges helps organizations build safer, more resilient AI deployments.
1. Unauthorized Access Risks
If authentication and authorization are not properly enforced, attackers may gain access to MCP-connected tools or data. Weak token management, shared credentials, or misconfigured roles can allow unauthorized users or AI agents to perform restricted actions.
Mitigation: Use OAuth 2.0, enforce RBAC, and apply least-privilege access.
2. Prompt Injection and Malicious Inputs
AI systems interacting through MCP may receive malicious prompts designed to manipulate tool behavior or extract sensitive data. Without strict validation, MCP servers might execute unintended commands.
Mitigation: Implement input validation, allowlisted actions, and context filtering.
3. Data Leakage and Privacy Concerns
MCP servers often handle confidential enterprise data. Improper logging, insecure storage, or overexposed APIs can lead to accidental data leaks.
Mitigation: Encrypt data in transit and at rest, mask sensitive logs, and enforce data access policies.
4. Insufficient Observability and Auditing
Without proper monitoring, suspicious activities may go undetected. Lack of audit trails makes it difficult to investigate incidents or ensure compliance.
Mitigation: Enable detailed logging, real-time monitoring, and compliance dashboards.
5. Integration Vulnerabilities
MCP servers connect to multiple external tools and services. A vulnerability in any integrated system can become an entry point for attackers.
Mitigation: Regularly scan integrations, apply security patches, and use trusted connectors.
6. Runtime Threats and API Abuse
Attackers may attempt denial-of-service attacks, excessive API calls, or exploit runtime weaknesses to disrupt services.
Mitigation: Apply rate limiting, Web Application Firewalls (WAF), and runtime threat detection.
Common Pitfalls With Securing MCP Servers
Many organizations focus on performance and integration but overlook critical security gaps. Understanding these common pitfalls helps you prevent data breaches, unauthorized tool usage, and compliance risks.
1. Excessive Permissions and Poor Role Design
Granting broad access to users, services, or AI agents increases the risk of misuse. Without proper role-based access control (RBAC), sensitive tools and data may be exposed.
Best practice: Enforce least-privilege access and define clear roles for every user and service.
2. Using Static API Keys and Long-Lived Tokens
Hardcoded credentials and long-lived tokens are easy to leak and difficult to manage. Once exposed, attackers can gain persistent access.
Best practice: Use OAuth 2.0, short-lived tokens, and automated key rotation.
3. Lack of Input and Schema Validation
Unchecked inputs can allow prompt injection, command manipulation, or unexpected tool execution.
Best practice: Enforce strict schemas, validate all inputs, and reject malformed requests.
4. Inadequate Logging and Monitoring
Without detailed logs and monitoring, suspicious activities may go unnoticed until damage occurs.
Best practice: Enable audit logs, real-time monitoring, anomaly detection, and alerting.
5. Prompt Injection and Tool Abuse
Attackers can craft prompts that trick AI into revealing sensitive data or executing restricted actions.
Best practice: Implement guardrails, allowlists, and human approval workflows for critical operations.
Summary: Checklist for MCP Server Security
Conclusion
MCP Servers are the new API boundaries for AI systems—and securing them is critical to prevent misuse, data leaks, or compliance failures.
By adopting authentication, RBAC, validation, observability, and runtime defenses, you can ensure your MCP servers remain resilient.
With the TrueFoundry MCP Gateway, enterprises get these best practices out-of-the-box, making it easier to deploy MCP securely while accelerating AI adoption.
Book a demo to know more.
Frequently Asked Questions
What are the best security practices for an MCP server?
Adopt a defense-in-depth strategy with strong authentication, RBAC, input validation, encrypted communication, and continuous monitoring. Use least-privilege access, rotate secrets, enforce schema validation, and deploy behind firewalls. Regular audits, patch management, and prompt-injection safeguards help prevent data leaks, unauthorized tool access, and compliance violations across AI-driven workflows and integrations.
How do you secure an MCP server in production?
Secure production deployments using private networking, TLS encryption, OAuth-based authentication, and centralized RBAC controls. Enable logging, rate limiting, and anomaly detection to monitor misuse. Isolate environments with VPCs or zero-trust architecture, apply automated patches, and validate tool inputs to prevent injection attacks, ensuring reliable and compliant AI operations at scale.
How does authentication work in MCP servers?
Authentication in MCP servers typically uses OAuth 2.0, OIDC, or signed tokens to verify users, services, and AI agents. Short-lived access tokens replace static keys, while identity providers manage trust. Mutual TLS and API gateways can add verification layers, ensuring only authorized entities access tools, data sources, and model capabilities.
How do you encrypt data in transit for MCP communication?
Encrypt MCP traffic using TLS 1.2+ to secure communication between clients, servers, and integrated tools. Implement HTTPS endpoints, certificate management, and mutual TLS for service-to-service trust. Use secure ciphers, rotate certificates, and enforce HSTS policies to prevent interception, tampering, and man-in-the-middle attacks during sensitive AI data exchanges.
TrueFoundry AI Gateway delivers ~3–4 ms latency, handles 350+ RPS on 1 vCPU, scales horizontally with ease, and is production-ready, while LiteLLM suffers from high latency, struggles beyond moderate RPS, lacks built-in scaling, and is best for light or prototype workloads.
The fastest way to build, govern and scale your AI






















.webp)
.png)


.webp)




.webp)
.webp)
.webp)
.webp)